vulnerable dependencies
Building modern software incorporates tons of code. We want sophisticated systems with great functionality and incorporating open source packages helps create them. Unfortunately in doing so, if a package that is implemented has itself a vulnerability, we’re introducing a vulnerability to potentially the entire system through that dependency. A good example of this is Struts, a framework for Java, which was the library responsible for the Equifax breach, with over 143 million consumers affected.
The Exploit
// ContentTypeHandler Java class in Struts
class ContentTypeHandler extends Interface {
ContentTypeHandler() {
this.hasQualifiedName("org.apache.struts2.rest.handler", "ContentTypeHandler")
}
}
//'toObject' method
class ToObjectDeserialzer extends Method {
ToObjectDeserializer() {
this.getDeclaringType().getASuperType*() instanceof ContentTypeHandler and
this.getSignature = "toObject(java.io.Reader,lang.Object)"
}
}
Sample code used to detect vulnerability
Pentest credits to Riyaz Walikar
Triggered by sending a malicious XML POST payload with the “Content-Type” header set to “application/xml”.
Equipped with adequate payload the vulnerability allows code execution on the server. Code executed doesn’t block the parent thread as it uses the java.lang.ProcessBuilder class. Executing time delay commands dont help.
(ping -n 20 127.0.0.1, sleep 5 etc.)
So, send network packets to a self-controlled server. Linux, wget or curl. Windows, ping your server and use tcpdump to check for incoming ICMP packets.
The ping command in this payload will send 10 ICMP requests to the server running tcpdump.
Run the following tcpdump command on your server.
tcpdump -nni yourinterface icmp
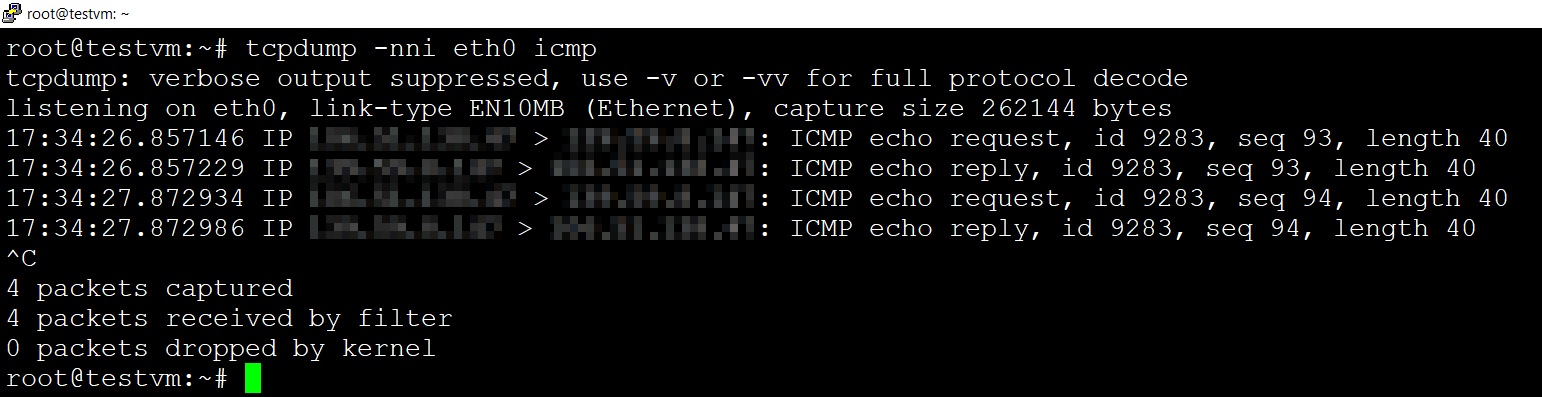
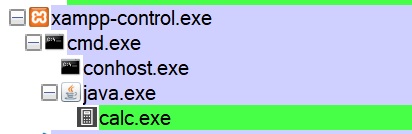
So it’s established the application is vulnerable, open up calc via shell commands to the server.
Richer Targets
Be cognizant of dependencies, don’t assume all supporting software products are flawless. Even if our system isn’t as attractive to attacks, we become a target by using a vulnerable framework since every organization using that framework is going to be vulnerable. Of course, the downside to an open source package is that anyone can read/reverse engineer it.
It’s not all rain, my friend.
In any case, tools are available to check for vulnerable dependencies like OWASP dependency check, npm audit, Retire.js, and more. More importantly, those dependencies should be updated and vetted on a consistent basis.